The Kimwolf botnet, a large network of compromised Internet of Things (IoT) devices, has recently caused significant disruptions to The Invisible Internet Project (I2P). I2P is an encrypted, decentralized network focused on anonymous communication. The issues began as Kimwolf’s operators started using I2P to protect their botnet’s control servers from being shut down.
Emerging in late 2025, Kimwolf rapidly compromised millions of vulnerable IoT devices, including streaming boxes, digital picture frames, and routers. These devices were then used to relay malicious traffic and launch exceptionally large distributed denial-of-service (DDoS) attacks.
I2P functions as a decentralized, privacy-centric network enabling anonymous communication and data sharing.
As described on the I2P website, data is routed through several encrypted layers via volunteer-run nodes, obscuring the locations of both sender and receiver. This creates a secure, censorship-resistant platform for private websites, messaging, and data exchange.
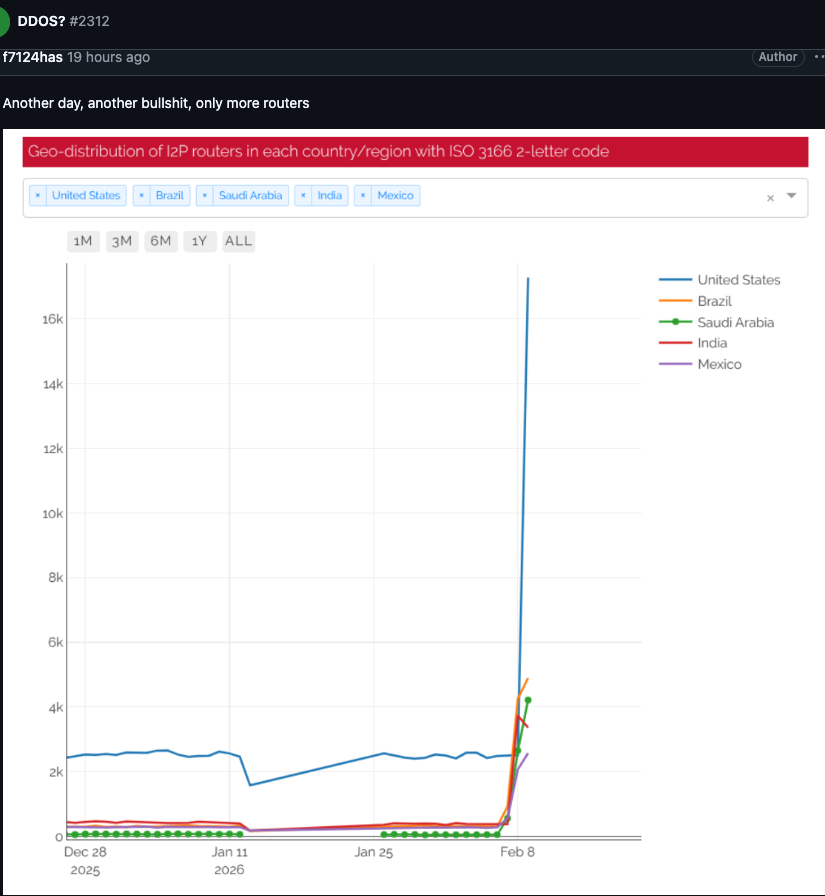
Starting February 3, I2P users reported issues on the network’s GitHub page. Tens of thousands of routers were suddenly flooding the network, hindering communication with legitimate nodes. The rapid influx of new, non-functional systems overwhelmed the network, making it impossible for users to connect.
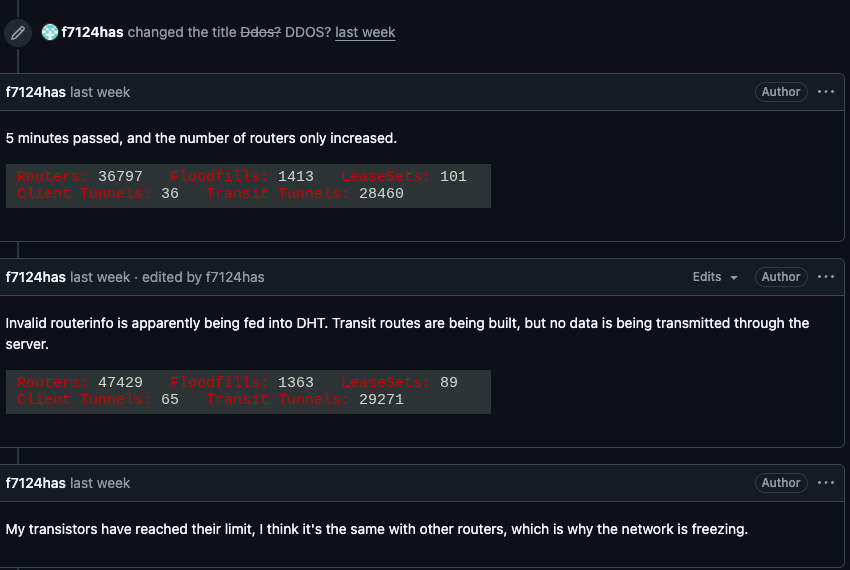
I2P users reported service disruptions due to a sudden surge of routers joining the network.
One I2P user questioned if the network was under attack, to which another responded, “Looks like it. My physical router freezes when the number of connections exceeds 60,000.”
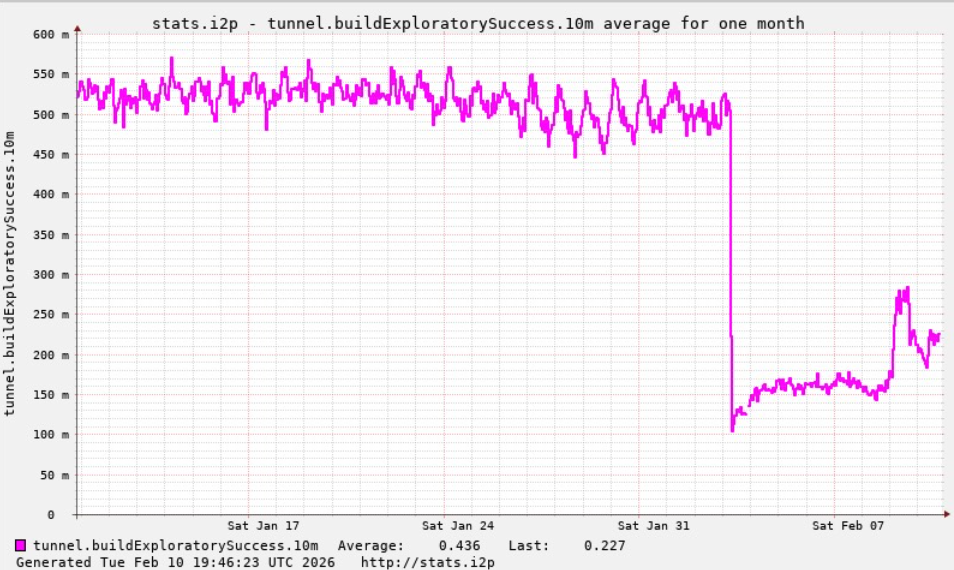
A graph from I2P developers illustrates a significant decline in successful network connections, coinciding with the Kimwolf botnet’s attempt to utilize the network for backup communications.
On the same day I2P outages were observed, the Kimwolf operators admitted on their Discord channel that they had inadvertently disrupted I2P. This occurred after they tried to add 700,000 Kimwolf-infected bots as network nodes.
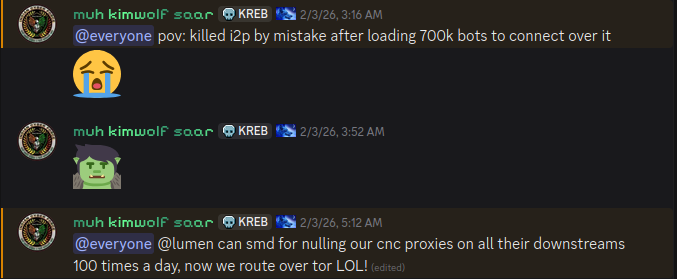
The Kimwolf botmaster openly discusses botnet activities in a Discord channel.
While Kimwolf is recognized for its powerful DDoS capabilities, the recent I2P outages, caused by a segment of the botnet attempting to join, represent a “Sybil attack.” This type of attack targets peer-to-peer networks, where a single attacker creates and controls numerous fake identities to disrupt the system.
The number of Kimwolf-infected routers attempting to join I2P significantly exceeded the network’s typical scale. According to Wikipedia, the I2P network usually comprises approximately 55,000 globally distributed computers, with each participant functioning as both a router and a client.
However, Lance James, founder of the cybersecurity consultancy Unit 221B and an original founder of I2P, stated that the I2P network currently operates with 15,000 to 20,000 devices daily.
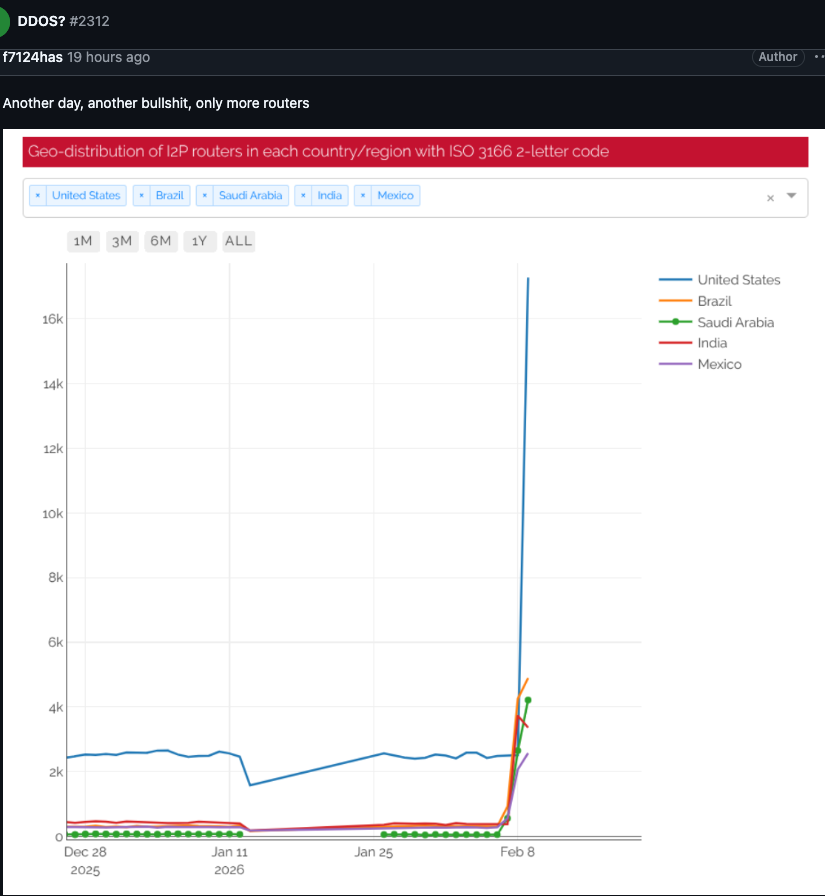
A graph posted by an I2P user on February 10, illustrating tens of thousands of routers, primarily from the United States, suddenly attempting to join the network.
Benjamin Brundage, founder of Synthient, a startup monitoring proxy services, was the first to document Kimwolf’s distinctive propagation methods. Brundage indicated that Kimwolf’s operators are attempting to establish a command and control network resistant to takedown efforts by security firms and network operators.
Brundage noted that Kimwolf’s controllers have been experimenting with I2P and the similar anonymity network — Tor — as a secondary command and control system. However, no recent widespread disruptions have been reported on the Tor network.
He suggested that the goal is not to disable I2P, but rather to find an alternative to maintain the botnet’s stability against takedown attempts.
Late last year, the Kimwolf botnet posed challenges for Cloudflare. It directed millions of compromised devices to use Cloudflare’s domain name system (DNS) settings, leading to Kimwolf-related control domains repeatedly displacing major companies like Amazon, Apple, Google, and Microsoft in Cloudflare’s public rankings of most requested websites.
James reported that the I2P network is currently operating at approximately half its usual capacity. A new release is being deployed, expected to enhance user stability within the coming week.
Brundage also noted that Kimwolf’s operators seem to have recently alienated some skilled developers, resulting in a significant error this past week. This mistake caused the botnet’s size to decrease by over 600,000 infected systems.
He commented, “It seems like they’re just testing stuff, like running experiments in production. But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing.”