Traditional phishing websites often consist of static copies of login pages, which are frequently detected and taken down by security entities. However, a sophisticated new phishing-as-a-service, known as Starkiller, bypasses these issues. It employs deceptive links to load the actual target website and then functions as a real-time relay, transmitting the victim’s username, password, and multi-factor authentication (MFA) codes to the legitimate site while forwarding its responses back to the victim.
While numerous phishing kits exist for aspiring scammers, their effective deployment often demands technical expertise in server configuration, domain management, and proxy services. Starkiller simplifies this process, dynamically loading a live version of the authentic login page, capturing user input, and relaying data between the legitimate site and the victim.
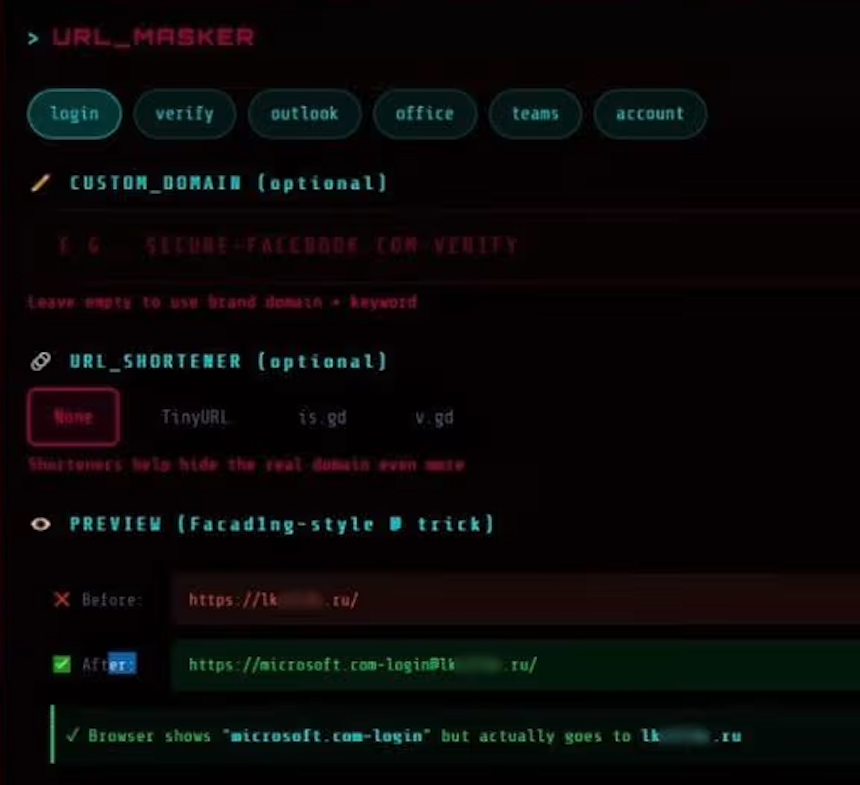
An analysis by the security firm Abnormal AI reveals that Starkiller allows its users to choose a brand to impersonate, such as Apple, Facebook, Google, or Microsoft. It then generates a misleading URL designed to visually resemble the legitimate domain, all while directing traffic through the attacker’s own infrastructure.
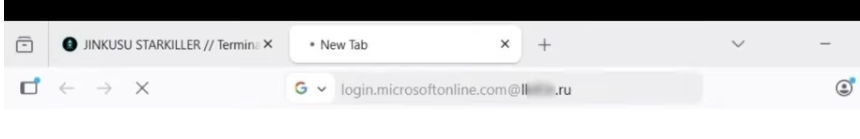
For instance, a phishing link aimed at Microsoft users might display as “login.microsoft.com@[malicious/shortened URL here].” The “@” symbol in the URL is a classic deception, as web browsers typically interpret everything before it as username information, with the actual destination being the address following the “@” sign. The following image illustrates how this appears in a browser:
Image: Abnormal AI. This illustration shows a blurred malicious landing page, which ends in .ru. The service also supports integrating links from various URL-shortening services.
Upon selecting a target URL, Starkiller initiates a Docker container that runs a headless Chrome browser instance to load the authentic login page, as discovered by Abnormal AI.
Researchers at Abnormal AI noted in a blog post that the container operates as a man-in-the-middle reverse proxy. It forwards user inputs to the legitimate site and relays the site’s responses back. This means every keystroke, form submission, and session token is captured and logged as it passes through the attacker’s infrastructure.
Starkiller provides cybercriminals with real-time session monitoring capabilities, enabling them to observe a target’s screen interactions with the phishing page live.
The platform’s features include keylogger functionality to capture every keystroke, theft of cookies and session tokens for direct account takeover, geo-tracking of targets, and automated Telegram notifications for new credential captures. It also offers comprehensive campaign analytics, such as visit counts, conversion rates, and performance graphs, mirroring the dashboards found in legitimate software-as-a-service (SaaS) platforms.
Abnormal AI highlighted that the service skillfully intercepts and relays a victim’s MFA credentials. Because the user is authenticating with the genuine site via a proxy, any submitted authentication tokens are immediately forwarded to the legitimate service.
This process allows attackers to capture session cookies and tokens, granting them authenticated access to the account. By relaying the entire authentication flow in real-time, MFA protections can be bypassed, even when they are functioning as intended.
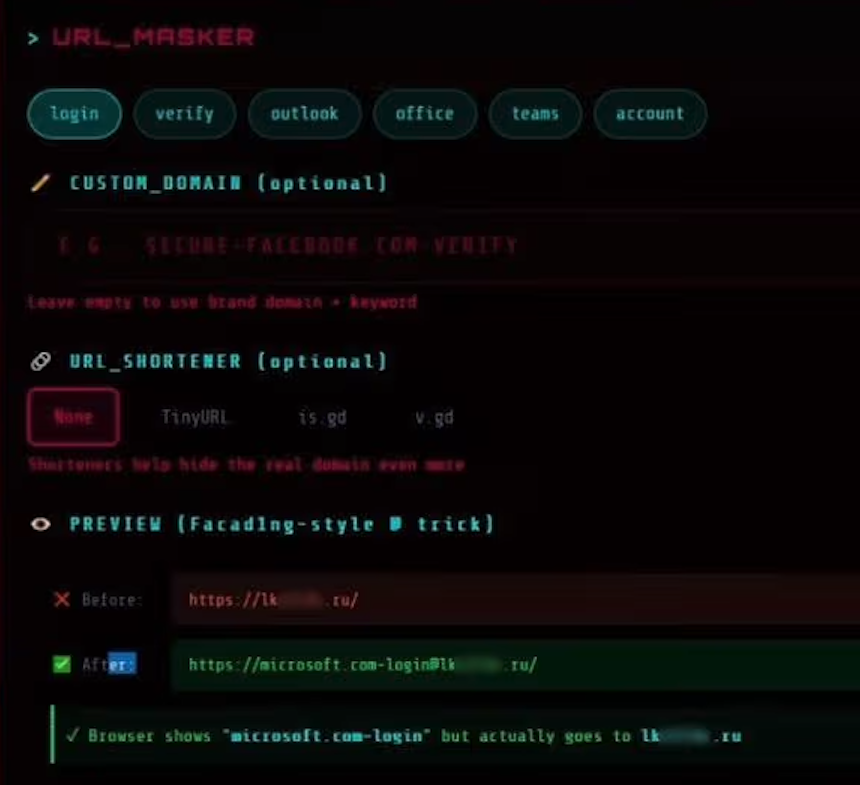
The “URL Masker” feature within the Starkiller phishing service provides various options for configuring malicious links. Image: Abnormal.
Starkiller is part of a suite of cybercrime services provided by the threat group known as Jinkusu. This group operates an active user forum where clients can exchange techniques, request new features, and resolve deployment issues. An optional feature offered by Jinkusu allows for the harvesting of email addresses and contact information from compromised sessions, which can then be utilized to create target lists for subsequent phishing campaigns.
This service represents a significant advancement in phishing techniques, and its reported effectiveness suggests it will likely be emulated by other cybercriminals. Such an approach eliminates the initial expenses and ongoing difficulties of managing numerous phishing domains, while also disrupting conventional phishing detection strategies like domain blocklisting and static page analysis.
Abnormal AI researchers noted that this service substantially lowers the barrier to entry for less experienced cybercriminals.
The Abnormal AI report concludes that “Starkiller represents a significant escalation in phishing infrastructure, reflecting a broader trend toward commoditized, enterprise-style cybercrime tooling.” The report further states that, “Combined with URL masking, session hijacking, and MFA bypass, it gives low-skill cybercriminals access to attack capabilities that were previously out of reach.”