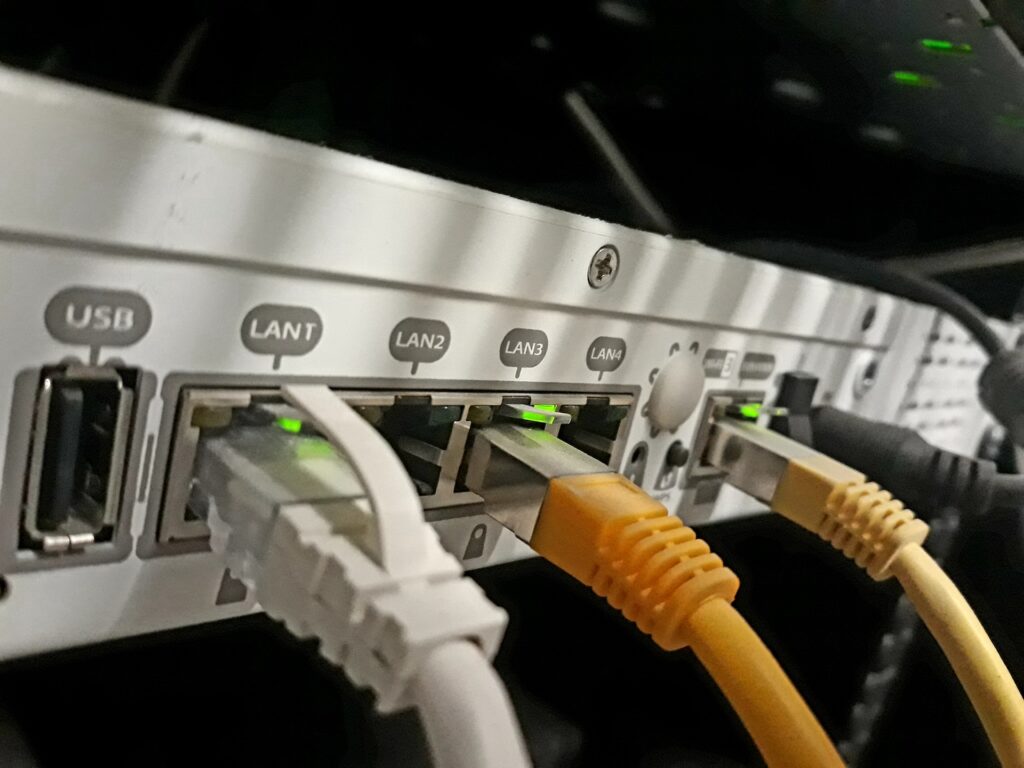
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a directive requiring federal agencies to cease using “edge devices” such as firewalls and routers that are no longer supported by their manufacturers.
This initiative aims to address a persistent and challenging attack vector for cybercriminals. This vulnerability has been implicated in some of the most significant and frequent exploits observed in recent years, with new edge-device vulnerabilities emerging regularly.
The binding operational directive mandates that federal civilian executive branch (FCEB) agencies must inventory all unsupported edge devices within their systems within three months. These devices, once identified on a specific list, must be replaced with supported alternatives within one year.
CISA Acting Director Madhu Gottumukkala stated that “Unsupported devices pose a serious risk to federal systems and should never remain on enterprise networks.” Gottumukkala emphasized that CISA will guide FCEB agencies to enhance cyber resilience and establish a more robust digital infrastructure. Non-federal organizations are also encouraged to implement similar measures to improve the security of their edge devices.
To assist agencies in complying, CISA is compiling a list of edge devices that have reached their end-of-service. This directive, developed collaboratively with the Office of Management and Budget, reinforces a ten-year-old OMB circular concerning the retirement of unsupported technologies by agencies.
Although termed “binding operational directives,” CISA lacks the authority to enforce these orders directly. However, agencies typically endeavor to comply, and CISA employs various methods to facilitate adherence. The private sector also monitors CISA’s directives, despite not being directly subject to them.
Nick Andersen, CISA’s executive assistant director for cybersecurity, explained that the directive focuses on collaboration with agencies to find solutions rather than forcing compliance. This approach considers situations involving operational technology that may be challenging to update or replace.
The directive highlights the “substantial and constant” threat to federal information systems from unsupported edge devices. These devices are particularly susceptible to newly discovered and unpatched vulnerabilities, offering potential access points for hackers.
According to the directive, “The United States faces persistent cyber campaigns that threaten both public and private sectors, directly impacting the security and privacy of the American people.” It further notes that “These campaigns are often enabled by unsupported devices that physically reside on the edge of an organization’s network perimeter.”
The directive references unspecified “recent public reports of campaigns targeting certain vendors,” indicating attempts by malicious actors to exploit these devices to gain access to FCEB information system networks. Andersen chose not to identify the specific reports but clarified that the order is not a reaction to a single incident or compromise.
Agencies are also required to establish a process within two years for the ongoing identification of edge devices that are, or will soon become, unsupported.
Andersen explained that the one-year deadline for decommissioning listed devices allows agencies sufficient time to invest in necessary new technology. CISA does not intend to make this list public.
This directive from CISA is being released almost exactly one year after the agency, in collaboration with other federal and international bodies, published guidance on safeguarding edge devices.