A recent surge in GoBruteforcer attacks has been observed, specifically targeting databases associated with cryptocurrency and blockchain initiatives. These attacks aim to incorporate the compromised systems into a botnet designed to brute-force user passwords for various services, including FTP, MySQL, PostgreSQL, and phpMyAdmin, on Linux servers.
According to an analysis by Check Point Research, this latest wave of campaigns is fueled by two primary issues: the widespread use of AI-generated server deployment examples that often include common usernames and weak default settings, and the continued presence of older web stacks like XAMPP, which frequently expose FTP and administrative interfaces without adequate security measures.
The GoBruteforcer malware, also known as GoBrut, was initially identified by Palo Alto Networks Unit 42 in March 2023. Early reports detailed its capability to target Unix-like systems across x86, x64, and ARM architectures. Its functions included deploying an Internet Relay Chat (IRC) bot and a web shell for remote control, as well as fetching a brute-force module to scan for and compromise additional vulnerable systems, thereby expanding the botnet.
In September 2025, a report from Lumen Technologies’ Black Lotus Labs team revealed that a significant portion of bots infected by the SystemBC malware family were also part of the GoBruteforcer botnet.
Check Point observed a more advanced version of the Golang malware in mid-2025. This updated variant includes a heavily obfuscated IRC bot, redeveloped in the cross-platform programming language, alongside enhanced persistence mechanisms, process-masking techniques, and dynamic credential lists.
The credential lists utilized by the botnet incorporate common username and password combinations, such as “myuser:Abcd@123” or “appeaser:admin123456,” which are often accepted for remote logins. These specific credentials are not randomly chosen; they frequently appear in database tutorials and vendor documentation. Consequently, these examples have been incorporated into the training data for Large Language Models (LLMs), leading LLMs to generate code snippets that include these same default usernames.
Other usernames found in the lists are either tailored for cryptocurrency-related targets (e.g., “cryptouser,” “appcrypto,” “crypto_app,” and “crypto”) or specifically aim at phpMyAdmin panels (e.g., “root,” “wordpress,” and “wpuser”).
Attackers reportedly employ a limited, consistent pool of passwords for each campaign, updating task-specific lists from this pool and regularly rotating usernames and specialized additions to target various systems. For FTP brute-force attacks, a distinct, hardcoded set of credentials is embedded directly within the bruteforcer binary, specifically targeting web-hosting stacks and default service accounts, unlike other services.
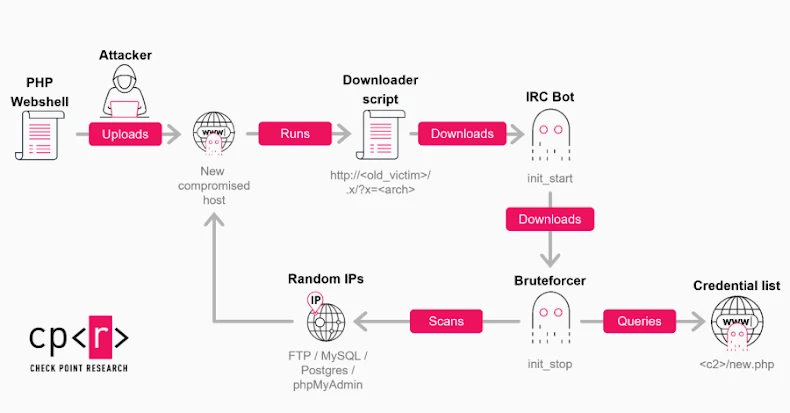
Check Point’s observations indicate that an internet-exposed FTP service on XAMPP-running servers serves as the initial entry point. This allows for the upload of a PHP web shell, which subsequently downloads and executes an updated IRC bot via a shell script tailored to the system’s architecture. Upon successful infection, a compromised host can fulfill three roles:
- Executing the brute-force module to attempt password logins for FTP, MySQL, Postgres, and phpMyAdmin across the internet.
- Hosting and distributing malicious payloads to other compromised systems.
- Serving as an IRC-style control endpoint or a backup command-and-control (C2) server for enhanced resilience.
Further analysis of the campaign revealed that one of the compromised hosts was used to deploy a module designed to iterate through a list of TRON blockchain addresses. This module queries balances via the tronscanapi[.]com service, specifically identifying accounts with non-zero funds. This activity highlights a focused strategy to target blockchain projects.
Check Point noted that GoBruteforcer illustrates a widespread and ongoing issue: the convergence of exposed infrastructure, weak credentials, and increasingly automated attack tools. Although the botnet’s technical complexity is relatively low, its operators exploit the large number of misconfigured services that are still accessible online.
This information emerges as GreyNoise reported that threat actors are actively scanning the internet for misconfigured proxy servers, which could potentially grant access to commercial Large Language Model (LLM) services.
Among two identified campaigns, one exploited server-side request forgery (SSRF) vulnerabilities to target Ollama’s model pull feature and Twilio SMS webhook integrations between October 2025 and January 2026. Given the use of ProjectDiscovery’s OAST infrastructure, this activity is believed to originate from security researchers or bug bounty hunters.
The second campaign, commencing on December 28, 2025, appears to be a high-volume enumeration effort. Its goal is to pinpoint exposed or misconfigured LLM endpoints linked to major providers such as Alibaba, Anthropic, DeepSeek, Google, Meta, Mistral, OpenAI, and xAI. The scanning activity was traced back to IP addresses 45.88.186[.]70 and 204.76.203[.]125.
The threat intelligence firm stated that, beginning December 28, 2025, two IP addresses initiated a systematic probe targeting over 73 LLM model endpoints. Within eleven days, these IPs generated 80,469 sessions – indicating a thorough reconnaissance effort to locate misconfigured proxy servers that could potentially expose commercial APIs.